Learning how to remember passwords is fun and easy.
Learning how to remember passwords is fun and easy.
But let’s take a step back before I give you some powerful memory training that may even help you retrieve a password you’ve lost.
I want you to promise that you’ll use the techniques on this page for memorizing your password, but still keep a backup.
This step is important because your passwords aren’t just about you. They’re also about your loved ones.
If anything should happen to you, they’ll need to access your accounts. And that means that just because it’s possible to memorize thousands of passwords if you wish, even the most accomplished memory champion still needs to back them up.
So with all that in mind, here’s what we’re going to cover in the post:
- How to turn passwords into stories and use linking
- Advanced mnemonics for memorizing numbers and symbols
- Using the Memory Palace technique to store many passwords at scale
- Making sure your memorized passwords enter long term memory
- Options for backing up your passwords to consider
But before we get into the memory techniques, we need to talk about password construction.
How to Set Safe Passwords You’ll Actually Remember
A lot of people bicker over what constitutes a “safe” password.
This is where each individual needs to reflect deeply on how they use the Internet and think through their needs.
For example, Samy Kamkar has suggested using song lyrics. He doesn’t go into great detail about how to do this, but it’s a compelling idea because you’re using something that you already know and won’t forget.
I would suggest changing vowels into numbers if you’re going to go this route. For example, if you’re going to use “What’s Going On” by Marvin Gaye, the letter “o” would become a 0. The password would then be whatsg0ing0n.
To add more uniqueness and complexity, you could turn the “s” into a “z” and capitalize it: whatZg0ing0n. If you’re required to add a symbol, you could cut the “a” in half and use a ^, making it wh^tZg0ing0n.

This approach may or may not be enough complexity to prevent software from cracking such a password, but that’s where each person needs to do their own research. But so far, wh^tZg0ing0n doesn’t look too simple, even if at its core, the original Marvin Gaye song is a password source many people will find impossible to forget.
For people who use the Internet sparingly, this approach is worth considering, though the technique does rely upon you knowing lyrics in the first place. It doesn’t have to be lyrics only, though. You can use book or movie titles, names of people, or any quote or set of words you can modify.
Nonetheless, there are times when you are given a password and cannot modify it. For that, you’ll want robust memory techniques. Let’s get started with one of the easiest.
Using the Story Method To Memorize Passwords
Let’s say you have to memorize a password like this: 90BHVdDRhaCu.
I would suggest going with the story method.
To use this unique mnemonic strategy, you would start with 90 and think about an association. For example, perhaps your grandfather is in his 90s.
You then start to imagine his 90th birthday party where you give your grandfather a beehive for a present, i.e. BHV. He loves it so much he puts a double-d battery in it (dD) and raps like a cupid.
To remember that it’s a capital “R” and “rap” is spelled with an “h,” you think about a giant rapper swimming in the Hudson River. Likewise, the cupid you imagine is giant.

At first glance, you might think this kind of storytelling is too much work and prone to error. However, most people do very well with it. The trick is to just let your imagination flow.
For another example of using stories like these in the context of how your memory works, check out my friend John Graham’s version of this for memorizing credit card numbers:
Using Advanced Mnemonics For Memorizing Numbers And Symbols
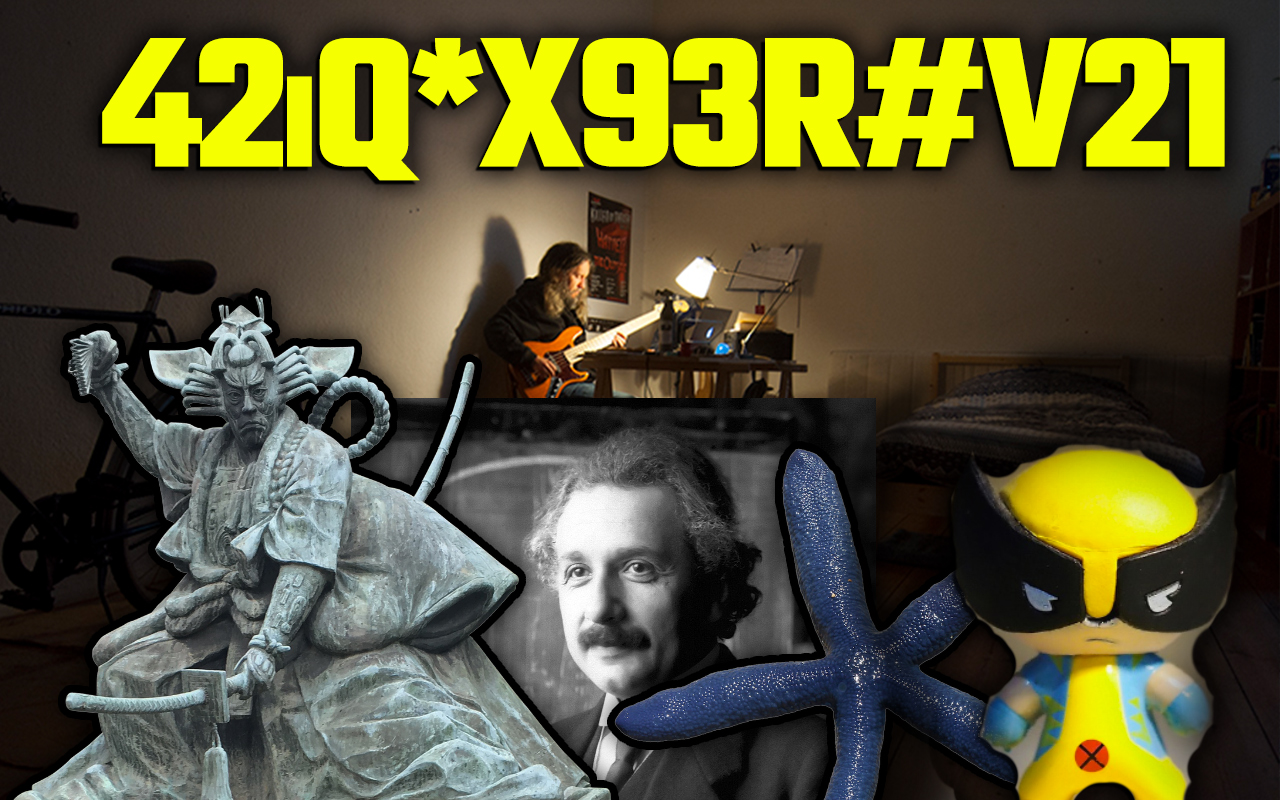
Now let’s say that you have to memorize a password like 42iQ*X93R#V21.
In this case, I would suggest you learn a technique called the Major Method and consider using it to develop a 00-99 PAO. I also suggest you develop an alphabet list using the pegword method.
In brief, the Major Method lets you associate a consonant with every digit from 0-9. You can then use those consonants to create words whenever you have at least two numbers in a row.
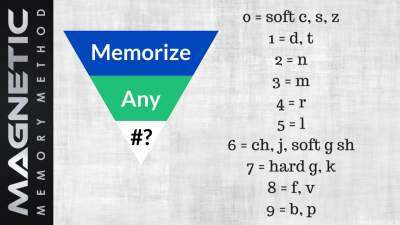
For example, a number like 42 becomes the word “ran.” I would use an image of a samurai from the movie Ran to make it concrete and specific.
Then, using an alphabet list, you will always have an image for each character of the alphabet. For example:
A = Apple
B = Bun
C= Cookie Monster, etc.
You can also have a double-alphabet. This is a much more involved memory tool to create, but useful if you want to stop forgetting things. In this case, you would generate images for two letters from AB to ZU:
Abacus
Accountant…
Zebra
Zulu
This method is only easy and efficient after some setup. But provided you base it on names you already remember, it’s a memory system that will reward you for many years to come. Memory athlete Brad Zupp shares more on the topic in this discussion we held about becoming a mental passwords manager on the Magnetic Memory Method Podcast:
Using the Memory Palace technique to store many passwords at scale
Having a lot of mental associations floating around randomly in your mind is bound to create confusion.
Enter the Memory Palace technique. It lets you store large amounts of information and recall them with ease.
To use the technique, I suggest you create a few Memory Palaces just for passwords.
Then, to memorize them, lay them out along a simple journey, like this:
To create a Memory Palace optimally, I suggest starting with a simple and familiar location.
Keep the task simple and focused by drawing a simple diagram to help train your mind to travel spatially in a refined manner. This simple program shows you how, including exercises that make sure you always have enough Memory Palaces for your passwords:
Making sure your memorized passwords enter long term memory
Whether or not you use the Memory Palace technique, you need to make sure that you get the passwords into long-term memory.
To do that, you need to practice bringing your passwords to mind. The Memory Palace makes the process easy because you can look into your mind and recall your images or the lyrics you used.
Aim to repeat the password at least five times per day until you’ve nailed it.
Again, keep a backup just in case. If you’re dealing with multiple passwords, you may want to draw simple mnemonic images on flash cards that remind you of the beginning of the sequence or story.
Obviously, you don’t want to give away too much on these cards. With some highly personalized material from you imagination, they should only make sense to you anyway. Or, you can store the cards in a secure location, like a safe. Because you always want to have a backup for the benefit of your loved ones, keeping a safe with your passwords in print is an idea worth considering.
How to Remember A Password You Forgot
Now that you know how to memorize new passwords, you might be wondering about recovering those you may have lost.
Some people think the brain stores information permanently and that you should be able to recover anything you used to know.
I’m skeptical of this claim because we know that memories are stored chemically in cells. Since cells die, it’s entirely possible that something you’ve memorized is gone if the chemicals that stored it die or get damaged.
That said, even with the many causes of forgetting we face, we also know it is possible to revive some memories. This means that you can potentially recall forgotten passwords by following a small set of steps:
- Get relaxed as deeply as possible
- Think back to where you were when you created or memorized the password
- Doodle or draw randomly to see if you can trigger ideas
- Imagine a keyboard in front of you and try to recreate how you used to type the password
You might also want to read the comments on the following video. A number of people have said that their passwords pop to mind while watching it:
What to Do If You Can’t Remember Your Password
There are a number of steps you can follow if you lose a password and absolutely can’t track your way back to it.
- Don’t panic. Getting stressed only causes your mind to shut down further.
- Take a deep breath. Go for a walk, stretch or meditate. Give yourself some distance.
- Widen your options. Where might you have stored it or where might you get a clue?
- Search and keep a record of the hunt. If you look through a document, jot down that you’ve checked it. Be thorough so that you can truly check it off and don’t waste time looking through the same locations multiple times.
- Reset the password if you can.
- Take steps to do better next time. When you get the password, store a backup and memorize it.
A lot of people think that technology for password managers are still premature, but for some people they’re necessary. For example, if you run a business and need to share logins with staff, a simple browser plugin can work wonders. Again, it’s important to do some analysis of your situation and work out what is best for you.
Remembering Cybersecurity Best Practices Using Mnemonics
Of course, there’s more to just keeping and remembering strong passwords. Make sure that you always:
- Enable two-factor authentication wherever possible
- Conduct regular software updates
- Practice safe browsing habits
- Regularly backup your data
Then there is a procedural memory process you can use to make sure you don’t fall prey to phishing attempts. For example, when you receive an email urging you to click a link, you can learn to habitually recite a little mantra:
Never click, always search manually
I do this often when I receive all kinds of outreach emails from people. Rather than click their links, I search their brand names and more often than not, find out they are not genuine.
To make this process even stronger, I sometimes pretend that I am a vigilant guard while reading my email. That, or a detective, watching for clues of something wrong.
In other words, I’m creating personalized memory cues. I recommend you do the same.
Helping Young People Remember Passwords
Many people ask me about teaching their kids memory techniques. Helping them learn mnemonics is a great way to do that.
In addition to helping them learn number mnemonics like we discussed above, you can play games with them.
For example, the Password Strength Game. Get them to create simple passwords during round one. Then, during round two, have them change the vowels to symbols and numbers. In other words, if they great “easterbunny” as a password, have them create a “power up” like in a video game, by changing it to “3aste4Bunn33.”
How to Remember Your Passwords For Life
It’s time to stop saying, “I can’t remember my password.”
There’s no doubt that using memory techniques is one of the most fast, easy and secure means of committing passwords to memory. With an appropriate means of backing up your memories, you’ll have the best of both worlds.
I suggest you commit yourself to learning these techniques and make sure you’re on board for putting security first. The Internet is only growing in complexity, and that means more passwords you’ll need to manage. The time to start developing good password management skills is now.
And using the skills you’ve just learned, you’re in a position to stop forgetting things forever.
Related Posts
- Long-Term Memory Loss: 5 Proven Ways to Stop It
Discover 5 proven, science-backed strategies to stop long-term memory loss, improve recall, and protect your…
- How to Remember Polyatomic Ions: The Ultimate Guide
Learning how to remember polyatomic atoms is easy and fun. Learn how to memorize at…
- How to Remember Where You Put Something in 5 Steps
If you want to know how to remember where you put something, you need expert…